Application Security & Gen AI
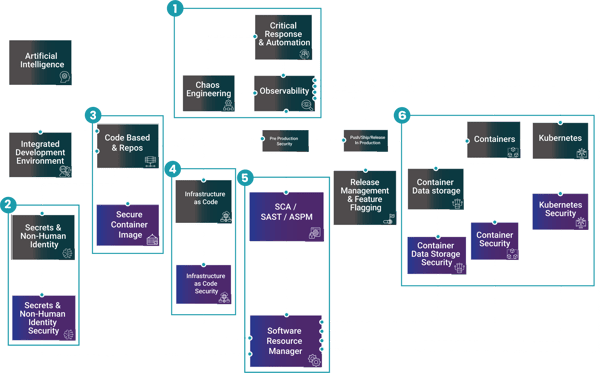
GenAI is changing how applications are built, developers can generate code faster, but it also amplifies software supply chain risk new dependencies, copied snippets, and inconsistent security patterns. Point tools can flood teams with findings, the future of AppSec is an integrated program that reduces noise and prioritises what matters.
Application Security (SCA, RASP, SAST, DAST, IAST & ASPM)
Building and releasing software often introduces vulnerabilities through custom code and open source dependencies and the rise of AI generated code can amplify risk and increase volume. Many teams also struggle with fragmented tools and noisy findings that are hard to prioritise.
The solution application security (SCA, RASP, SAST, DAST, IAST & ASPM) deciphers this by scanning source code and compiled artifacts to identify vulnerabilities early, then correlating and prioritising results so teams can remediate issues before they reach production.
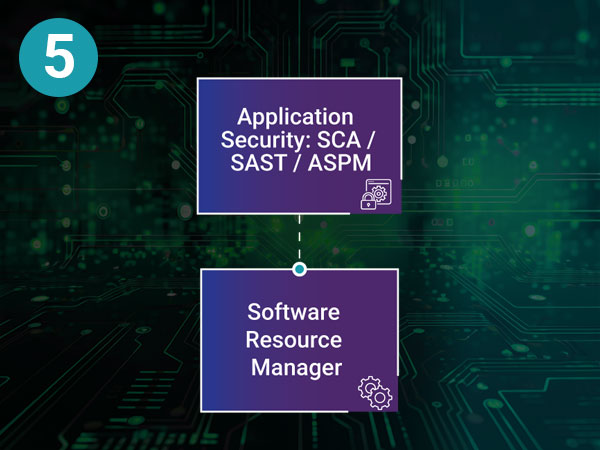
Application Security (SCA, SAST & ASPM)
Problems
Building applications introduces code vulnerabilities, and adding AI amplifies these risks—especially in an industry crowded with fragmented tools rather than holistic solutions.
Solution
Application Security tooling can scan the code or software that has been complied to check for any vulnerabilities that can be fixed before being introduction into production.
Software Risk Manager
Security teams are often overwhelmed by alerts scattered across multiple tools, forcing them to manually search for context and decide what matters most. This slows response times and increases the chance that critical risks are missed.
The solution a software risk manager solves this by aggregating signals across the security stack, correlating related findings, and prioritising the highest impact risks so teams can focus efforts on what truly threatens production.
Software Resource Manager
Problems
Lot’s of alerts in individual tooling, manual searching.
Solution
Prioritises security risks across security stack.
Firstly...
First, shift security into the developer workflow. Sysdig/BlackDuck/Invicti adds AI powered workflows to help teams find, prioritize, and fix issues early. Black Duck strengthens software composition analysis by identifying open source and third party components, enforcing policy, and producing SBOMs plus the ability to trace copied or AI generated snippets back to source projects.
Finally...
Bring context and validation Apiiro/Invicti’s ASPM layer applies a contextual, risk based approach to correlate and prioritize risks across the SDLC, and Sysdig/BlackDuck/Invicti validates real exposure with DAST against running web applications and APIs.
Together, these platforms enable secure, AI accelerated delivery without slowing engineering.
Industry Awards


Sysdig rated a Strong Performer in Gartner® Voice of the Customer for Cloud-Native Application Protection Platforms.

JFrog Named as a Visionary in the 2025 Gartner® Magic Quadrant™ for Application Security Testing.

The Application Security Market has exploded in recent years following the whole push to cloud, Agentic AI and LLM’s producing more code than ever. It’s predicted to grow to over $25B by 2030 with a CAGR of between 12-20%. Companies who have brought into SCA, RASP, SAST, DAST, IAST & ASPM products are now seeing those same products be very specific to a singular use case and therefore needing to think more about end-to-end platforms. This is most true in full scale enterprise & government customers.
![]() Financial services/FinTech
Financial services/FinTech![]() Insurance
Insurance![]() Healthcare
Healthcare![]() Public sector
Public sector![]() Telecommunications
Telecommunications![]() Energy
Energy![]() Retail/Ecommerce
Retail/Ecommerce ![]() Technology/SaaS/ISVs
Technology/SaaS/ISVs ![]() Transportation/Logistics
Transportation/Logistics
Roles
Who cares about The future of Application Security & GenAI?
![]() Platform Engineering Manager
Platform Engineering Manager![]() CISO/Head of Security
CISO/Head of Security![]() Head of Application Security (AppSec)
Head of Application Security (AppSec)![]() Product Security Lead
Product Security Lead![]() VP Engineering/CTO
VP Engineering/CTO![]() Platform Engineering Manager
Platform Engineering Manager![]() Developer Platform Owner
Developer Platform Owner![]() DevSecOps Lead/CI/CD Owner
DevSecOps Lead/CI/CD Owner
Key Discovery Questions
|
1 |
Are developers using GenAI coding assistants today, and what guardrails exist (secure patterns, review controls, policy)? |
|
2 |
How do you currently find and manage risk across code, open source dependencies, containers, and APIs and is “too many findings” a problem? |
|
3 |
Do you have a single source of truth for artifacts and images, and do you scan + gate what gets pushed into production? |
|
4 |
Are you generating SBOMs today, and can you meet customer or regulatory expectations for provenance and compliance? |
|
5 |
How do you validate real exploitable issues in running apps (DAST) and ensure findings map to owners, with measurable remediation time? |
Continue Your Journey
Contact Us
Connect with our global team
As technology continues to reshape industries and deliver meaningful change in individuals’ lives, we are evolving our business and brand as a global IT services leader.










