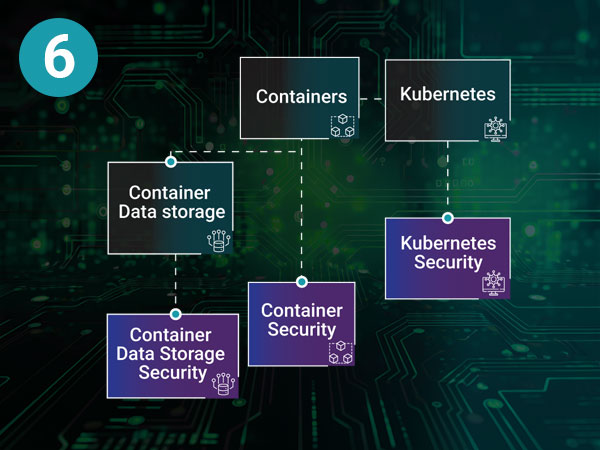
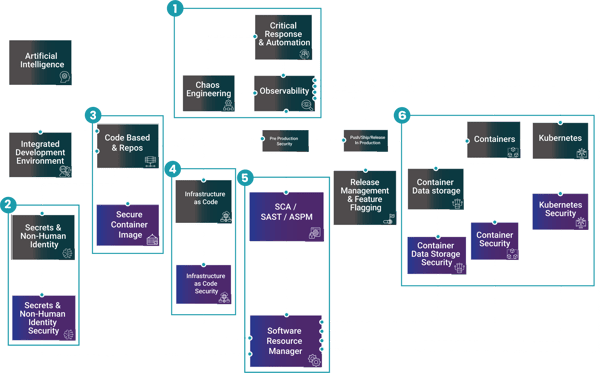
Securing Containers, Kubernetes & Data
Containers and Kubernetes accelerate delivery, but they also expand the attack surface: vulnerable images, misconfigured clusters, and overly broad access to data can turn a small mistake into a breach. Our approach secures the container lifecycle from developer workstation to production runtime.
Containers
Traditional applications often rely on inconsistent dependencies and tightly coupled, monolithic architectures that are difficult to deploy and scale reliably. This creates “it works on my machine” issues and slows down delivery across environments.
The solution containers solve this by packaging an application and its dependencies into a portable, consistent unit shifting from “pets” to “cattle” so teams can deploy the same build anywhere, scale predictably, and modernise services more safely.
Containers
Problems
Different dependencies, monolithic architecture.
Solution
Cattle vs Pets packaging apps and dependencies together.
Container Data Storage
Container and Kubernetes data storage can be complex to manage, difficult to scale, and expensive especially when teams need persistent volumes, backups, and recovery across multiple clusters and environments. Without a consistent approach, data protection becomes manual and unreliable.
Container data storage solutions address this by automating and unifying how data is provisioned, protected, and recovered for modern applications, helping teams reduce operational overhead, improve resilience, and control costs as they scale.
Container Data Storage
Problems
Container and Kubernetes storage can be complex and costly.
Solution
Automate, protect, and unify data for modern applications in containers and Kubernetes.
Kubernetes
Running containers is easy at small scale but managing them across multiple services and environments quickly becomes complex. Teams struggle with scheduling, scaling, failover, updates, and maintaining reliability as demand changes.
The solution Kubernetes solves this by orchestrating containers at scale automating deployment, scaling, and recovery so applications run consistently and reliably, even as infrastructure and workloads grow.
Kubernetes
Problems
Managing Containers at scale.
Solution
Orchestration and scaling for containers, making sure they run reliably.
Start...
with governance at the source. Docker provides Hardened Docker Desktop controls like Registry Access Management and Image Access Management so developers can only pull from approved registries and vetted image types. Then protect what you run: Sysdig secures containers and Kubernetes with runtime aware vulnerability management, compliance automation, and real time threat detection.
Finally...
harden the supply chain and distribution with Mirantis. Mirantis Secure Registry (MSR), built on the Harbor project, includes RBAC, image signing, and CVE scanning, and Mirantis Kubernetes Engine adds an extra layer of threat protection that travels with your applications across environments.
Together, Docker + Sysdig + Mirantis reduce risk without slowing delivery.
Industry Awards

Real-life stories. Powered by Docker.
Celebrating developers and organisations reaching their potential.

Mirantis Recognized as a Challenger in the 2025 Gartner® Magic Quadrant™ for Container Management.

Mirantis Builds Momentum for Kubernetes-Native AI Infrastructure - businesswire news.

It's predicted that by 2030, the market opportunity with be circa $10B for technology companies in the Container Management and Kubernetes space, including the security and runtime of those same deployment. This is massively being driven by the rise of cloud native application deployment with it now being estimated that 90% of companies are already using or planning to use Kubernetes.
Customers are looking at building own developer platforms, using managed services to run their containers and Kubernetes clusters or now looking to refine their day 2 operations. It's really just a question of where they are in their journey & this is something we're seeing across all major industries.
![]() Financial Services
Financial Services![]() Healthcare
Healthcare![]() Public Sector
Public Sector![]() Telecommunications
Telecommunications![]() Energy
Energy![]() Retail/Ecommerce
Retail/Ecommerce
Roles
Who cares about Securing Containers, Kubernetes & Data?
![]() Platform Engineering Manager
Platform Engineering Manager![]() Kubernetes Platform Owner
Kubernetes Platform Owner![]() DevOps/SRE Lead
DevOps/SRE Lead![]() Cloud/Kubernetes Architect
Cloud/Kubernetes Architect![]() Cloud Security Architect
Cloud Security Architect![]() Security Engineering Lead
Security Engineering Lead![]() CISO/Head of Security
CISO/Head of Security
Key Discovery Questions
|
1 |
Where are you running containers and Kubernetes today (managed cloud, on prem, hybrid), and what are your biggest security concerns in production? |
|
2 |
How do you control which images developers and pipelines can use (approved registries, curated images, signing/scanning)? |
|
3 |
Do you have runtime threat detection and response for Kubernetes workloads and how quickly can you investigate what happened? |
|
4 |
How do you measure and enforce Kubernetes security posture (RBAC, policies, misconfigurations, compliance reporting) across clusters? |
|
5 |
What is your current approach to protecting sensitive data in container platforms (access controls, secrets, and audit visibility), and where are the gaps? |
Continue Your Journey
Contact Us
Connect with our global team
As technology continues to reshape industries and deliver meaningful change in individuals’ lives, we are evolving our business and brand as a global IT services leader.






