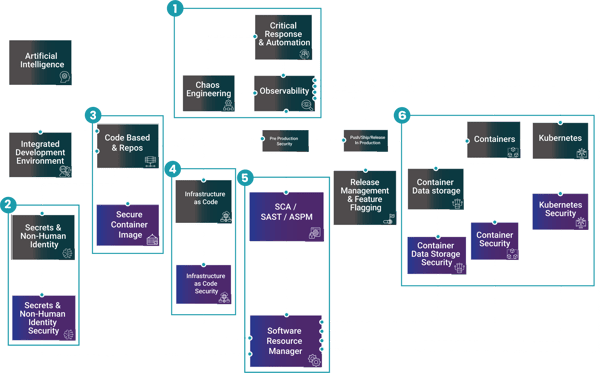
Securing your Codebase, Repo's & Images
Modern software development teams move fast to build and ship as quickly as possible. However, the trade-off for speed is risk, when using publicly available code from codebases like GitHub or images from registries like DockerHub or Jfrog’s Artifactory, they can contain vulnerabilities across source code, open source packages, dependencies and container images.
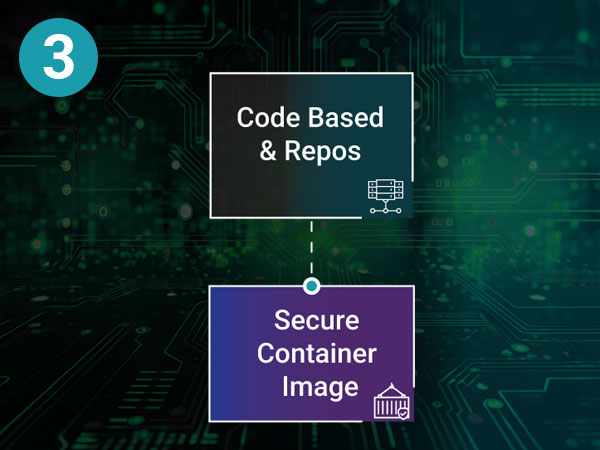
Code base & Repos
As teams grow, codebases often become fragmented across silos, with inconsistent version control and changes that are poorly tracked or undocumented. This leads to rework, bugs, and delivery delays.
The solution, codebase and repository management provides strong version control and collaboration, giving teams a single source of truth where changes are tracked, reviewed, and shared so teams can build software together with confidence.
Code base & Repos
Problems
Building Siloed, No version control, Untracked changes
Solution
Version control and collaboration, so everyone works on the same source of truth and changes are tracked.
Secure Container Images
Standard container images pulled from public registries can introduce hidden vulnerabilities, outdated packages, and compliance risk into the software supply chain. Developer & Compliance teams lack visibility into this which creates an attack surface across the end-to-end developer supply chain.
From 2025, it started to become necessary to fix these vulnerabilities in accordance with compliance initiatives like DORA and NIS2. The aim for Enterprise and Government customers is to seek to reduce or have 0-CVE's in the digital software supply chain.
Secure Container Images
Problems
Using standard container images may invite vulnerabilities
Solution
Using Docker Hardened Images ensures that developer are using updated, secure and compliant container Images maintained by Docker.
Industry Awards

Real-life stories. Powered by Docker.
Celebrating developers and organisations reaching their potential.


Cyber Security Excellence Awards: recognised in the category Software Supply Chain Security.

Every single industry worldwide is adopting a more digital orientated approach which dictates the need for ever growing developer & engineering functions. Large & small customers are seeing the need for secure development in their supply chains.
The larger the organisation typically means the larger the challenge and more complex the requirements, combined with the number of applications being built and according to Gartner, 45% of companies will be subject to a supply chain attack by 2025.
Roles
Who cares about securing Codebase, Repo's & Images?
Key Discovery Questions
|
1 |
How do you currently manage the security of your code, dependencies, and container images? |
|
2 |
Do you allow developers to use public images? |
|
3 |
Are your dev teams using different pipelines, tools, or image sources? |
|
4 |
When was the last time you reviewed your software supply chain risk? |
|
5 |
Do you feel you have full visibility from code commit to production runtime? |
Continue Your Journey
Contact Us
Connect with our global team
As technology continues to reshape industries and deliver meaningful change in individuals’ lives, we are evolving our business and brand as a global IT services leader.





